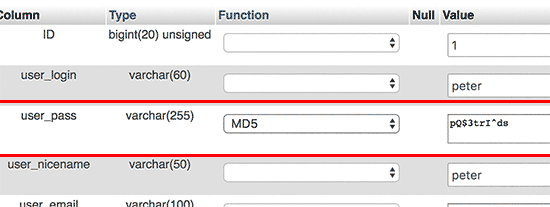
Very useful tip from this post:
http://www.wpbeginner.com/beginners-guide/how-to-reset-a-wordpress-password-from-phpmyadmin/
Thank you!

What's new in web design and development – Principal: Paul D. Gurney.
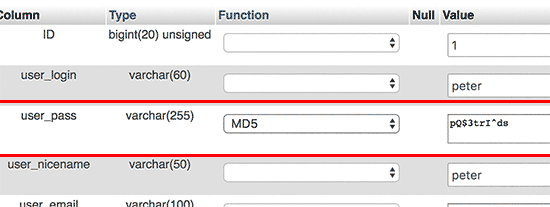
Very useful tip from this post:
http://www.wpbeginner.com/beginners-guide/how-to-reset-a-wordpress-password-from-phpmyadmin/
Thank you!
From an excellent Ars Technica article: Choosing between MySQL and NoSQL.
http://arstechnica.com/information-technology/2016/03/to-sql-or-nosql-thats-the-database-question/
“For 30 years in the IT industry, we’ve had traditional development models,” Gnau said. “We grab users, put them in a room, get their requirements, build out the design, look for data to find structures and reporting, implement and hand it back to users. It was a traditional waterfall approach. Even agile development starts with requirements and winds up with results.
“In Hadoop, you need to challenge that and turn it around. Data is not structured. Users may not know what the requirements are. It’s an inverse process—you land the data, find data scientists to find relationships that are interesting and appealing, and turn that into requirements that yield a system. It’s the opposite approach to a traditional process.”
This bookmarklet is useful to view source in Safari on Apple’s iPad. There is no built-in menu tool to do this in iOS, unlike with all desktop browsers. Oh why, Apple, do you drift ever further from user-centric software development?
Here is the link to the article by Ole Michelsen.
http://ole.michelsen.dk/blog/view-source-on-the-ipad-and-iphone/
A fine solution is to create a bookmarklet, which is a piece of JavaScript saved as a bookmark. When you want to see the source of a web page, just click the bookmark and the source of the page is displayed. I was inspired by this bookmarklet by Rob Flaherty, but it has a few shortcomings. To improve upon the bookmarklet concept, I created my own version with a few more bells and whistles:
On April 8 I was notified by WiredTree, our hosting company, that their servers had been patched against a newly discovered (and serious) flaw in the SSL encryption technology which underpins secure browsing over https.
It is called the Heartbleed bug.
Our servers were not affected, as they ran CentOS5 and did not use Litespeed. Other sites which did use LiteSpeed were affected.
Read more at:
http://heartbleed.com/
https://blog.cloudflare.com/staying-ahead-of-openssl-vulnerabilities
UPDATE
An article on Thursday explains how the bug crept in the Open Source software.
Heartbleed, a “catastrophic” security flaw in the OpenSSL cryptographic protocol that has affected two-thirds of the entire Internet’s communications, was committed at 10:59 pm on New Year’s Eve by Seggelmann, a 31-year-old Münster, Germany-based programmer.
That night, he made an error that has been compared to the misspelling of Mississippi, a careless but almost inevitable mistake that went undetected for over two years.
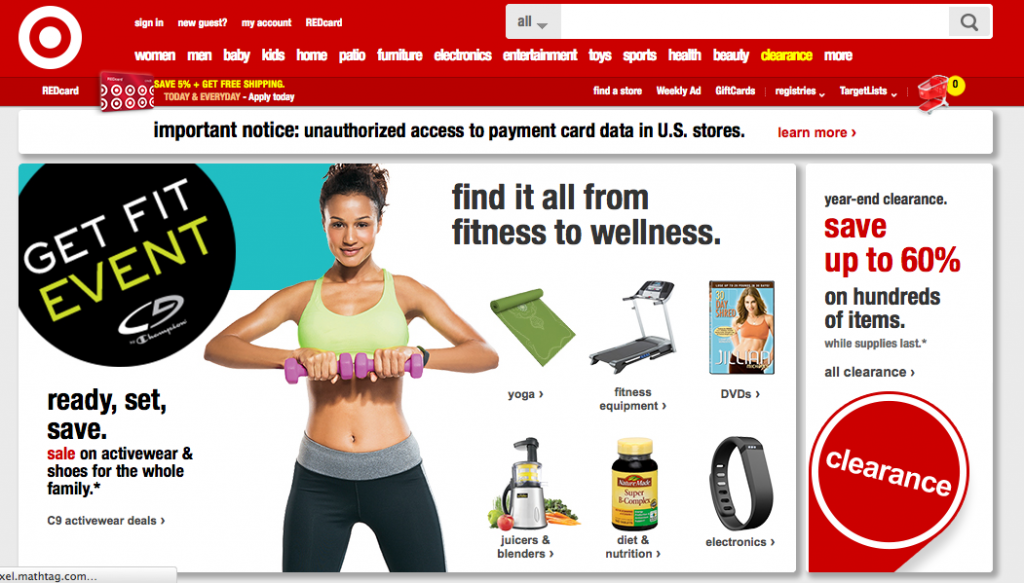
Target’s had a big red target leveled at its data systems recently; the intrusion and theft of over 100 million consumer credit & debit card information is almost the largest in history.
It’s website features a notice to consumers; but strangely, 2 seconds after the home page loads, an ad overlay obscures the warning text and link.
Purposeful or by accident, it’s a big oops on top of the disaster.
See the site 1 second after load:
And 2 seconds later:
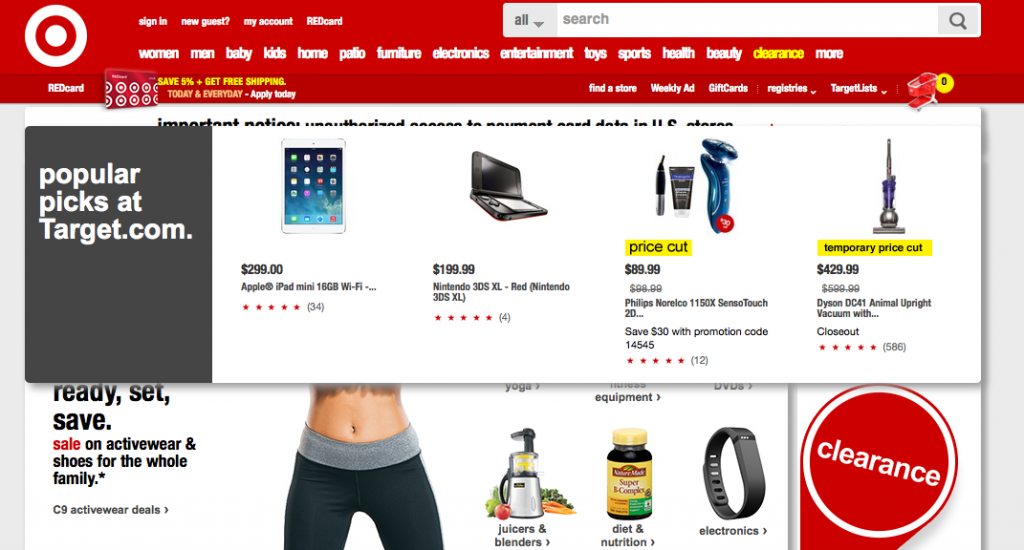
Intentional or by accident?
Does the law require companies to disclose breaches?
As an aside, most States do not require the companies disclose successful network breaches to their customers. A law firm has published a useful chart to track State-by-State requirements.
http://www.perkinscoie.com/statebreachchart/
The write:
Perkins Coie’s Privacy & Security practice maintains a comprehensive chart that summarizes state laws regarding security breach notification. The chart is for informational purposes only and is intended as an aid in understanding each state’s sometimes unique security breach notification requirements. Lawyers, compliance professionals, and business owners have told us that the chart has been helpful when preparing for and responding to data breaches.
Maine has such a disclosure law on its book.
Google acknowledged (and fixed) a major vulnerability in its google.com and gmail.com domains.
Redirection, cross-site scripting, cross-site request forgery, and SQL-injection vulnerabilities are to websites what dandelions are to suburban lawns. Even sites maintained by experienced and highly vigilant Web developers are likely to suffer from these Web-application bugs.
From ArsTechnica. Read more here.
Gmail removes the entire HEAD portion of your email’s HTML. It will also remove any STYLE elements. However, you can easily overcome this limitation by inlining your CSS using one of many online tools:
MailChimp’s CSS Inliner
TorchBox Apps Inliner Styler
MailerMailer Magic CSS Inliner Tool
This article on 10 things you MUST know before you register a domain name with anyone
is useful: http://www.domainwarning.com
That’s why we recommend Hover.com for domain name purchases.
If you have a blog, you need to install this plug-in immediately.
http://wordpress.org/extend/plugins/limit-login-attempts/
There is currently a major type of internet attack being waged by botnets against webservers running WordPress. These bots brute-force their way in past your password screen by making thousands of guesses until they gain entry. WordPress currently does not limit the number of incorrect password attempts. Until it does, you need a plug-in that provides the limiting.
There is currently a significant attack being launched at a large number of WordPress blogs across the Internet. The attacker is brute force attacking the WordPress administrative portals, using the username “admin” and trying thousands of passwords. It appears a botnet is being used to launch the attack and more than tens of thousands of unique IP addresses have been recorded attempting to hack WordPress installs.
One of the concerns of an attack like this is that the attacker is using a relatively weak botnet of home PCs in order to build a much larger botnet of beefy servers in preparation for a future attack. These larger machines can cause much more damage in DDoS attacks because the servers have large network connections and are capable of generating significant amounts of traffic. This is a similar tactic that was used to build the so-called itsoknoproblembro/Brobot botnet which, in the Fall of 2012, was behind the large attacks on US financial institutions.
Source: http://blog.cloudflare.com/patching-the-internet-fixing-the-wordpress-br